Jan. 29, 2026
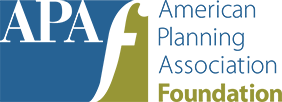
This past September, contractor Rochon Corporation received good news about its bid to install a digital sign at a Minneapolis middle school. An email apparently from city planner Ben Carrier said the company's sign variance was recommended for approval, and if Rochon paid an attached invoice for $4,800, it could avoid administrative delays on the way to final authorization.
The email noted that instructions for wiring payment would be sent separately, since "all correspondence associated with this case must be conducted via email" for "accountability, transparency, and ease of auditing."
Rochon Corporation's staff quickly clocked the message as a fake. Although Carrier was a real person, his email address wasn't Planning-Dept.CityOffMinneapolisMN@usa.com. While the other details of the request were spot on, a fee of that amount — paid through a wire transfer, of all things — was not standard operating procedure, since the city relies on in-person or over-the-phone credit card payments.
Since May 2025, a growing number of phishing emails have hit inboxes throughout Minneapolis, says city planning director Meg McMahan, AICP. "It just stuck out to us, because the amount of detail that they had was alarming," she says.
Phishing attempts on the rise
This new form of phishing — using public planning data to compose counterfeit emails requesting money — has gone nationwide. In many cases, the phishing emails come within hours or days of public meetings or website postings.
According to news reports and interviews with planning officials, dozens of departments have reported such attempts, from small cities like Martinsburg, West Virginia, to Miami, Houston, and Las Vegas.
Several planners say these emails are increasingly sophisticated, with seemingly official seals, references to municipal and state statutes, and phony signatures. However, there are tells — like odd payment requests, subpar graphic design, and fake email addresses. Several cities also have reported the use of the @usa.com domain.
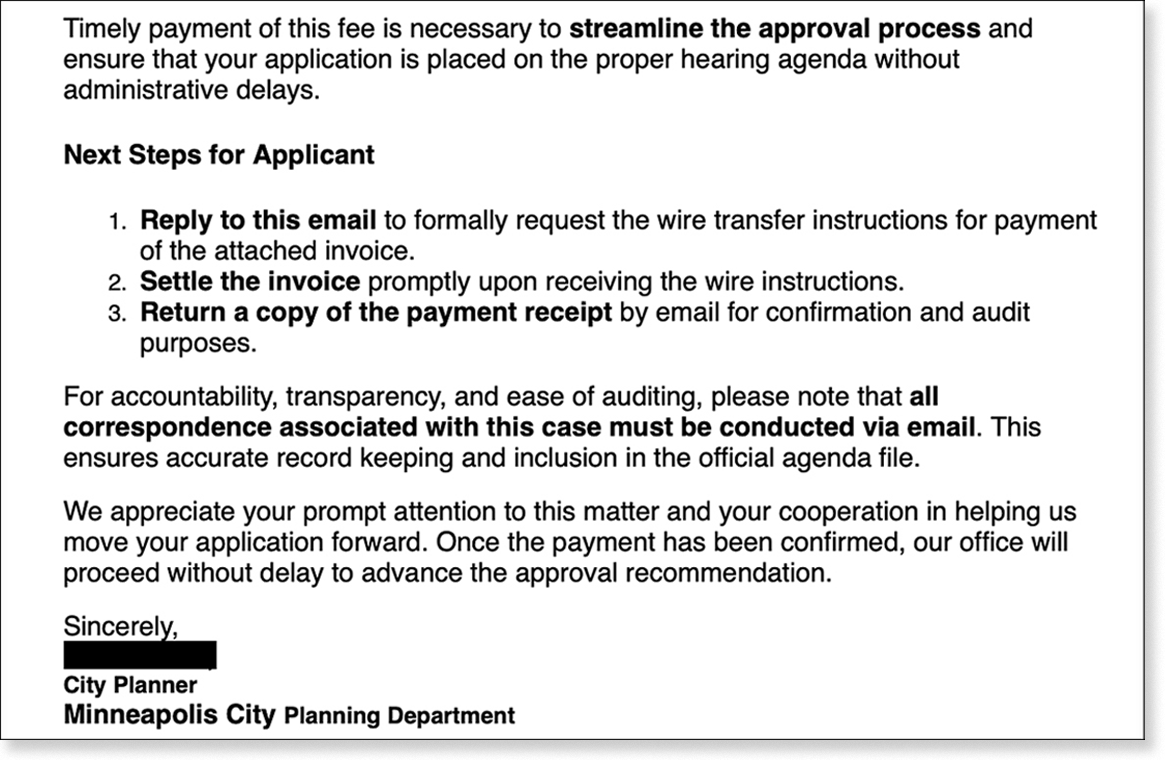
An email, excerpted above, requesting a variance application fee be paid via wire transfer was quickly shared with Minneapolis' Community Planning and Economic Development Department — who the scammer was impersonating. Image courtesy of City of Minneapolis.
In Montclair, New Jersey, the local detective bureau is investigating phishing attempts that used the @usa.com domain, according to Montclair Local. David Genova, principal of Greenwood Development, a local real estate development firm, was confused when a fake email requesting a wire transfer appeared in his inbox late last year.
"I've done 30-plus projects in town, and I've never seen an email like this, and I've already paid my application fees and escrow fees, so I went, 'What is going on here?'" Genova told the news outlet.
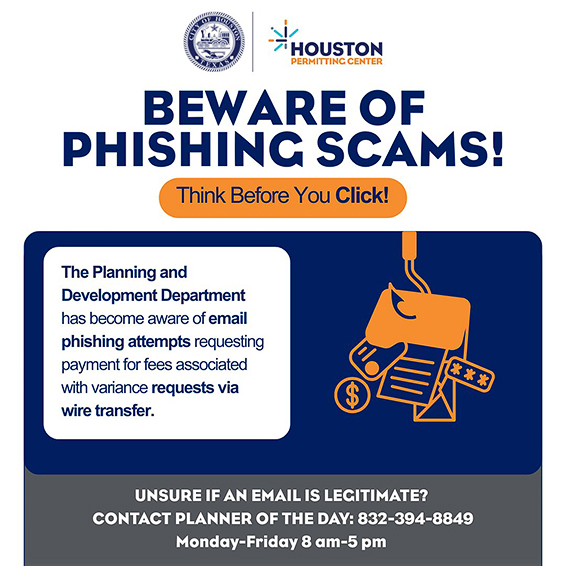
One planner in Oskaloosa, Iowa, however, reports that a local business fell for the scam, wiring payment to a fake organization supposedly based in Colorado. The applicant paid an alleged planning department invoice for a rezoning application, but soon after received a second invoice. Confused, they called the department to sort it out and learned the first one was a scam.
"It's like punishment for these applicants for doing the right thing," says Shawn Christ, AICP, the city's development services director. He was especially frustrated that his name was used in the fake email. "It just looks bad on everybody," Christ says.
What does this mean for the future?
In response, many planning departments have altered their operations to warn developers and residents about these phishing attempts. Many suspect — but can't definitively prove — artificial intelligence (AI) is being used.
They also question whether this tactic may erode the public's trust. "Balancing that tension is something that's worrisome to me, especially when I think about the potential for the sophistication of this sort of thing to escalate," says McMahan of Minneapolis.
Cybersecurity training has become standard for municipal workers, as the prevalence of these cons increases. FBI data estimated phishing scams cost victims at least $70 million in damage — but many incidents go unreported, so the amount could be even more.
In Miami, the police department is investigating a series of phishing emails to see if internal databases were breached or email accounts were hacked, says Erica Lee, assistant to the director of the city's planning department. Earlier in 2025, the planning department was made aware of about a dozen poorly composed phishing emails requesting thousands of dollars in payment. As the year progressed, similar scam emails became more polished, with details apparently scrubbed from the city's website and the names and dummy signatures of real officials.
Is AI an accomplice?
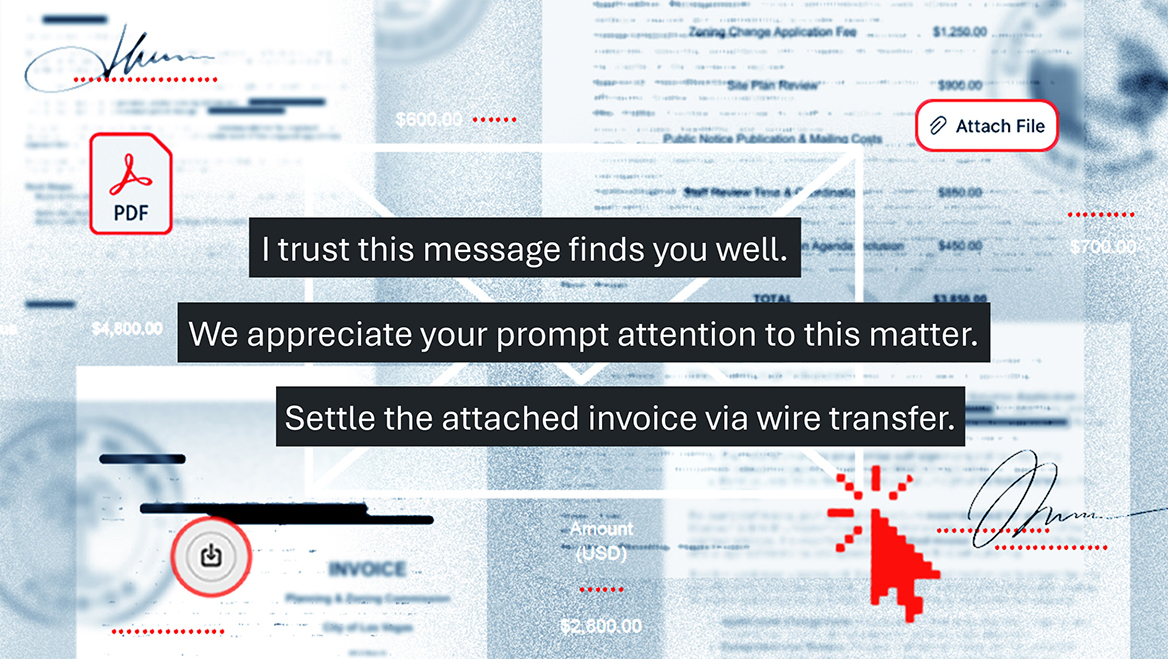
Suvidha Bandi, AICP, planner manager for Houston, has seen similar scam emails on and off since May 2025. Like the emails flagged in Minneapolis and Miami, these fake invoices urge recipients to respond for wire payment instructions.
"It's no coincidence that an uptick in this sort of thing, and phishing in general, coincides with an uptick in the adoption of generative AI," says Joseph Avanzato, a security operations and forensics team leader for the Varonis cybersecurity firm. Varonis has tracked a roughly 700 percent increase in phishing attacks throughout 2025, and a 200 percent increase in phishing attempts using generative AI.
Municipalities are targeted because of their significantly large workforces and because they oversee a lot of payments, says Phillip Harmon, a cybersecurity and data privacy associate at Woods Rogers.
While it's hard to get commercial AI programs and large-language models to do something illegal, Avanzato says, scammers can simply set up their own local AI models, train them on thousands of invoices and local planning and building codes, and set them loose.
Most cities don't report such attempts, Harmon says, and the amounts requested — sometimes amounting to a few thousand dollars — don't necessarily capture the attention of law enforcement.
Fighting back with information
Many of the affected cities have deployed or are creating information campaigns to deter further phishing scams. In Minneapolis, the planning department quickly added warnings to its pre-application process, so applicants are aware of who would contact them and the right way to pay.
Planners also teamed up with the city's IT department for a campaign warning residents about these scams. In Miami and Houston, officials also have reviewed their application processes to inform applicants pre-emptively of the right channels for communication and payment.
These scams show the potential downside to increased transparency that may allow others to use information for sinister purposes. As technology allows bad actors to create even more personalized, detailed cons at scale, the issue of transparency will only become more crucial.
"This isn't the answer people want to hear, but for these criminals, it's a business," says Harmon. "They're money-motivated. If there is an increase in any of these types of attacks, it's because they've worked, right?"
While technology to spot and deter scams continues improving, concentrating on the human element — training users in official channels of communications and how to avoid such scams — remains the better deterrent, Harmon says.
"This might be the unfortunate case where you just don't have a technological fix," he says. "The fix is not to make the data available, but that's not an option if departments are required to be publicly transparent."